Somewhere in your system right now there's a login that belongs to someone who no longer works for you.
Maybe they left on good terms. Maybe they didn't. Maybe they were let go on a Friday afternoon and were out the door before anyone thought to call IT. Maybe there was no IT to call — just a managed services company that handles tickets when you submit them, not problems they proactively prevent.
Either way, the access is still there.
Their email might be forwarding somewhere. Their credentials might still open your project files, your accounting software, your client database. If they were in payroll, they might still see salaries. If they were in estimating, they might still see your numbers and so might whoever they work for now.
I've walked into hundreds of businesses over 15 years of IT assessments and this is one of the most common things I find. Business owners assumed their IT company was handling it. Their IT company assumed someone internally was handling it. Nobody was handling it.
The space between what you assume is being managed and what's actually being managed, is where most IT problems live.
Here's what makes this one particularly dangerous: it's invisible. Most common IT problems announce themselves, but an ex-employee with active credentials just sits there quietly, posing a major security risk that takes you off-guard.
And when that day comes, when a disgruntled former employee leaks a client file, or a competitor gets access to your bid numbers, or your cyber insurance company asks you to document your offboarding process and you realize you don't have one, that cost can be more than financial. It'll be the relationships you spent years building.
The construction industry runs on trust. Your clients trust you with their projects, their timelines, their money, and their reputation. They assume the company they hired has its own house in order. The ex-employee problem is a quiet betrayal of that trust.
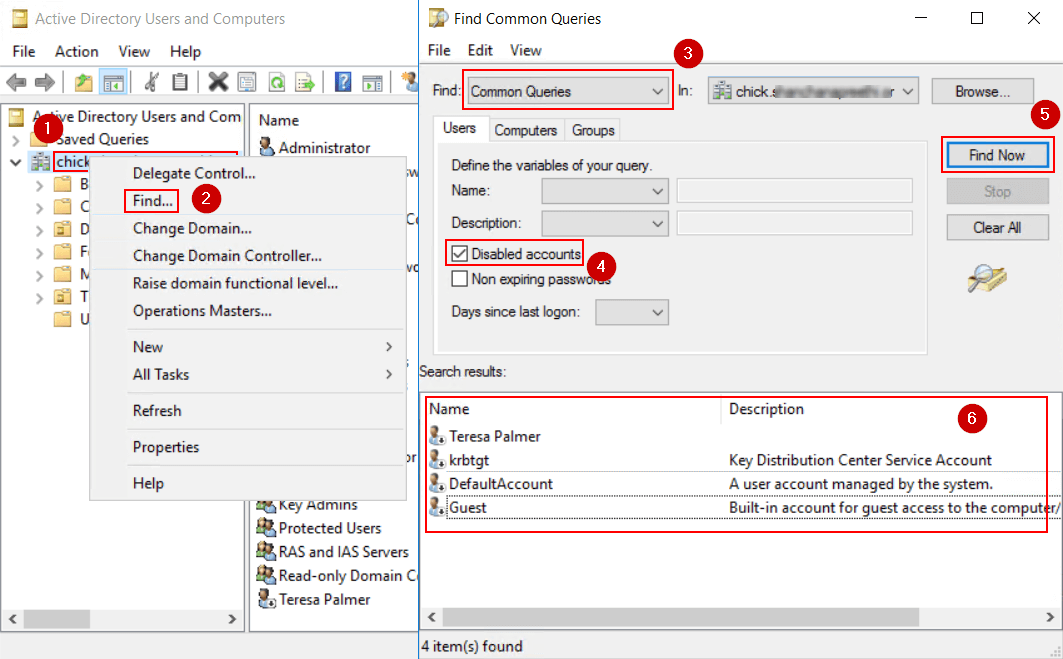
Find disabled users
The fix is easy. Every time someone leaves your company — voluntarily or not — their access gets revoked the same day. Email, software, VPN, shared drives, everything. It’s best practice and it is required to be a good steward of your information and your customers’ information.
Take this week to audit your computer user list. Make sure your employee and contractor accounts are properly maintained.
Until next week,
—Jared
Text Me: 314.806.3912
How To Support Me
Let me send this directly to your inbox every week, subscribers also receive special events and downloads that I don’t publish anywhere else.
Smart starts here.
You don't have to read everything — just the right thing. 1440's daily newsletter distills the day's biggest stories from 100+ sources into one quick, 5-minute read. It's the fastest way to stay sharp, sound informed, and actually understand what's happening in the world. Join 4.5 million readers who start their day the smart way.